3. Design Requirements¶
The key words “MUST”, “MUST NOT”, “REQUIRED”, “SHALL”, “SHALL NOT”, “SHOULD”, “SHOULD NOT”, “RECOMMENDED”, “MAY”, and “OPTIONAL” in this document are to be interpreted as described in RFC 2119.
3.1. Usernames and Passwords¶
Usernames
The client SHOULD assume that each user has a unique username.
Usernames are case-sensitive:
Bobandbobare different users.Usernames can be any length greater than zero (they CANNOT be empty).
Passwords
The client MUST NOT assume each user has a unique password. Like the real world, users may happen to choose the same password.
The client MAY assume each user’s password generally is a good source of entropy. However, the attackers possess a precomputed lookup table containing hashes of common passwords downloaded from the internet.
3.2. User Sessions¶
The client application MUST allow many different users to use the application at the same time. Each user runs a client program on their own device, which connects to the servers. For example, Bob and Alice can each run the client application on their own devices at the same time.
The client MUST support a single user having multiple active sessions at the same time. For example, user
bobcan run the client application on his laptop and tablet simultaneously. Each ofbob’s sessions, call themS1andS2, would be created by a call toGetUser()with the same credentials. All file changes MUST be reflected in all current user sessions immediately (i.e. without terminating the current session and re-authenticating). Here are some examplesAfter
bobstores a fileF1in sessionS1, sessionS2must be able to downloadF1.After
bobappends toF1in sessionS1, sessionS2must be able to download the updated version.After
bobreceives a fileF2viaReceiveFile()in sessionS1, sessionS2must be able to downloadF2.
The client DOES NOT need to support concurrency. Globally, across all users and user-sessions, all operations in the client application will be done serially.
3.3. Public keys¶
Each public key SHOULD be used for a single purpose, which means that each user is likely to have more than one public key.
A single user MAY have multiple entries in Keystore. However, the number of keys per user MUST be a small constant; it MUST NOT depend on the number of files stored or length of any file, how many users a file has been shared with, or the number of users already in the system.
3.4. Stateless¶
3.5. Files¶
Any breach of IND-CPA security constitutes loss of confidentiality.
The client MUST ensure confidentiality and integrity of file contents.
The client design MAY leak the size of file contents.
The client MUST ensure the confidentiality and integrity of filenames.
Filenames MAY be any length, including zero (empty string), but the client design MAY NOT leak the length of any filename.
The client design MAY leak the number of files associated with a user.
The client MUST NOT assume that filenames are globally unique. For example, user
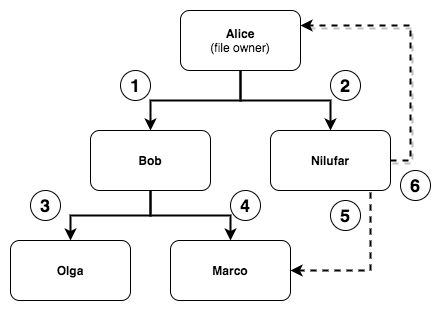
bobcan have a file namedfooand useralicecan have a file namedfoo. Though there is a single instance of the Datastore server that is used by all users, the client application MUST keep each user’s file namespace independent from one another.The client MUST enforce authorization for all files. The only users who can access a file include: (1) the owner of the file; and (2) users with whom the file has been shared and not revoked.
Changes to the contents of a file MUST be available to all users who are currently authorized to load the file. In other words, changes to the contents of a file MUST NOT change who the file is shared with.
The following SHOULD be avoided because they are dangerous design patterns that often lead to subtle vulnerabilities. We test for them and treat any instance of them as a breach of confidentiality/integrity.
reusing the same key for multiple purposes (e.g. encryption, authentication, key- derivation, etc); and
authenticate-then-encrypt; and
decrypt-then-verify.
3.7. Efficiency¶
The client MUST allow users to efficiently append new content to previously stored files.
We measure efficiency in terms of the bandwidth used by the
AppendFile()operation (the total size of the data uploaded and downloaded via calls toDatastoreGet()andDatastoreSet()).The bandwidth of the
AppendFile()operation MUST scale linearly with only the size of data being appended and the number of users the file is shared with, and nothing else. Logarithmic and constant scaling in other terms is fine.For example, appending 100 B to a 10 TB file should not use 10 TB of bandwidth. The 1,000th and 10,000th append operations to the same file should not use significantly more bandwidth than the 1st append operation. This is not an exhaustive list of restrictions.
AppendFile()is the only function that has an explicit requirement for efficiency. However, the client MUST implement other functions such that they do not time out the autograder (e.g. they cannot be grossly inefficient).You can submit to Gradescope as often as you like to verify whether your tests finish within the allotted time (usually about ~10 minutes max).
3.8. Access Tokens¶
Any breach of IND-CPA security constitutes loss of confidentiality.
The client MUST ensure the confidentiality and integrity of the secure file share invitations pointed to by accessTokens generated by
ShareFile().The client SHOULD assume that users share accessTokens with each other directly via the User Communications detailed in the Threat Model. You do not need to implement the passing of accessToken from one user to another. You just have to implement the
ShareFile()andReceiveFile()functions according to their defined APIs.
3.9. Golang¶
The client application code MUST NOT use global variables (execpt for basic constants).
Your Go functions MUST return an error if malicious action prevents them from functioning properly. Do not panic, do not segfault; return an error.
Return
nilas the error iff an operation succeeds. Return a value other thannilas the error iff an operation fails.